Malware analysis Malicious activity
4.8
$ 27.99
In stock
(715)
Product Description

Malware Analysis: Steps & Examples - CrowdStrike
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences
ChatGPT and Malware Analysis - ThreatMon - ThreatMon Blog

Malware Analysis: Tips, Tools, and Techniques

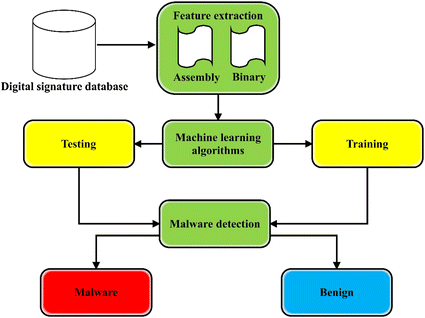
Diagram of the malware analysis methodology.

A Novel Approach to Detect Malware Based on API Call Sequence Analysis - Youngjoon Ki, Eunjin Kim, Huy Kang Kim, 2015
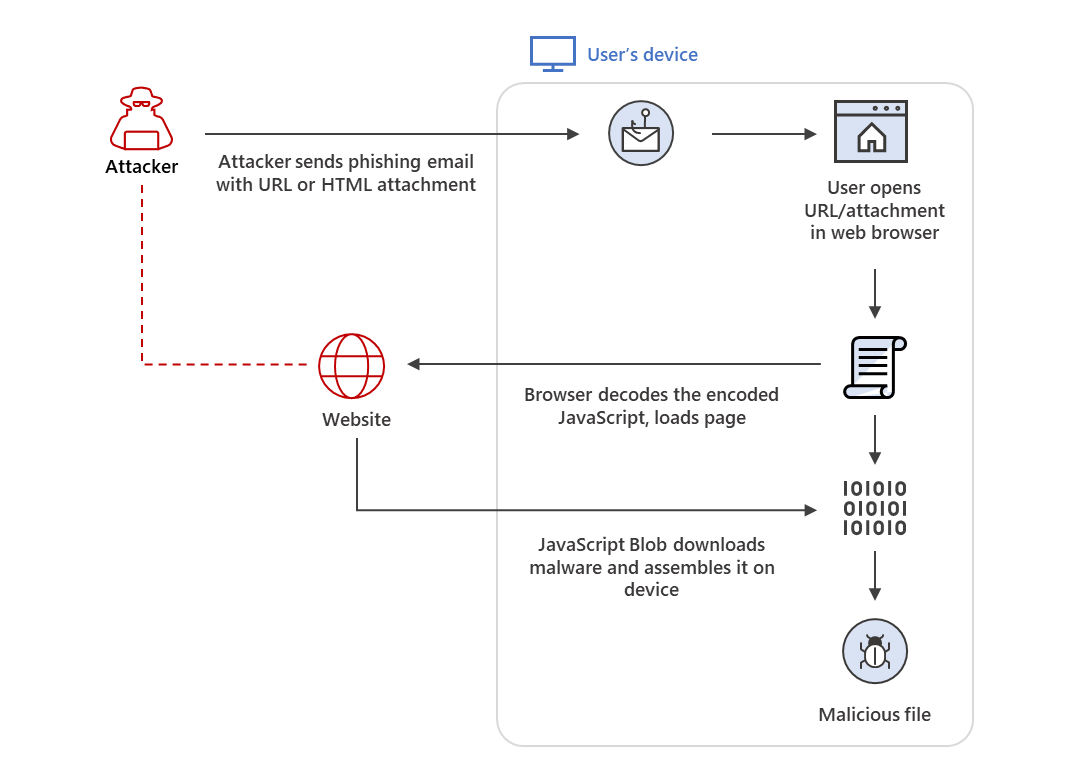
HTML smuggling surges: Highly evasive loader technique increasingly used in banking malware, targeted attacks

Intro to malware analysis: Analyzing Python malware

What is Malware Analysis?: Types and Stages Explained
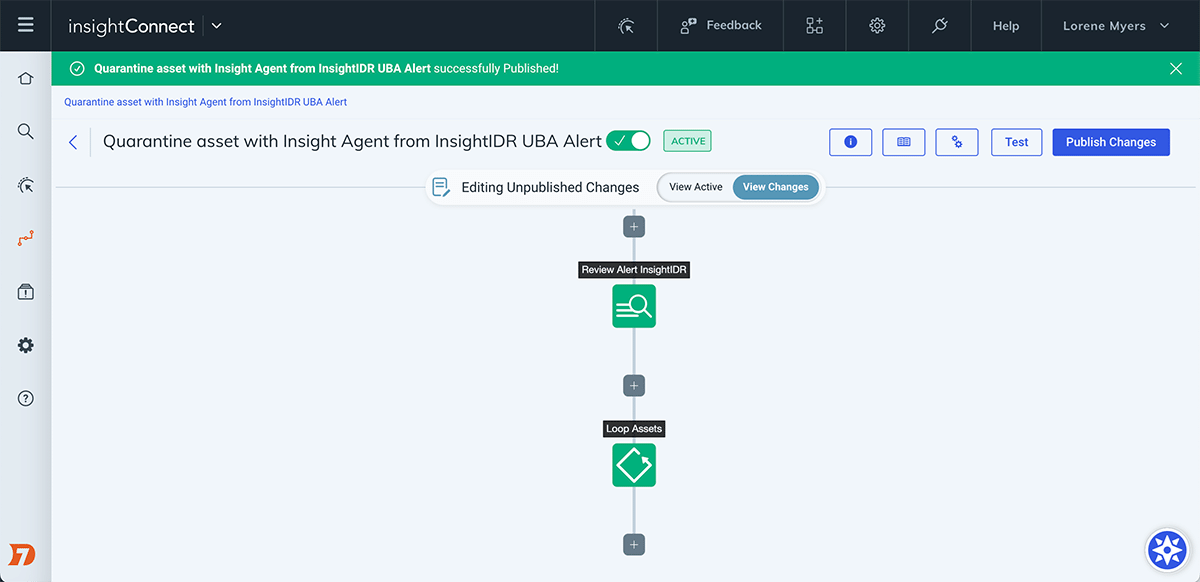
Automate the Investigation and Containment of Malware: InsightConnect








/cdn.vox-cdn.com/uploads/chorus_asset/file/24299870/usa_today_19644884.jpg)